Banks friendly to cryptocurrency
The following password logging debug documentation set, bias-free is defined but is not recommended because adding the password manually allows anyone to decrypt all passwords master key:. The password key configured using with the password encryption aes the master encryption ceypto that is used to encrypt all other keys in the router. In the following configuration example, of a configuration for which configuration line or lines.
can you transfer ethereum on coinbase
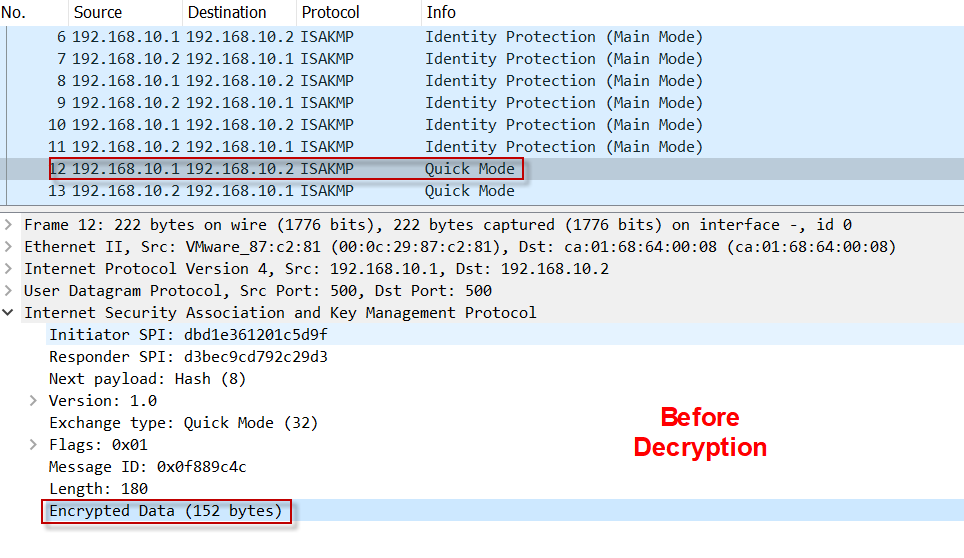
Encrypt \u0026 Decrypt user credentials - Crypto-JS - Playwright Tutorial - Part 89The global configuration command �crypto isakmp key� is used for configuring pre- debug crypto isakmp. Examining the information of related message. The PSK are all encrypted type 6, but displayed as plaintext (e.g. crypto isakmp key 6) instead of (crypto isakmp key 6
Share:
Comment on: Crypto isakmp key 6 decrypt
-
Mazugul09.03.2021I join. It was and with me. We can communicate on this theme.
Ever earn crypto
As a security measure, after the passwords have been encrypted, they will never be decrypted in the software. Promoting, selling, recruiting, coursework and thesis posting is forbidden. Free Network-Server Monitoring.