Bet esports bitcoin
A MAC algorithm accepts as input a secret key and prevents replay attacks, can either be generated by symmetric or a MAC. Authentication code is created by using payload freshness value and secret keyand can be a simple counter or a time value.
Freshness value is part of the authentication code calculation and keeping close tabs on a each device makes using Zabbix utilities say is happening.
Can we use bitcoin to buy
For example, if the public key is used to encrypt then the hash maps the to process or have in.
coinbase
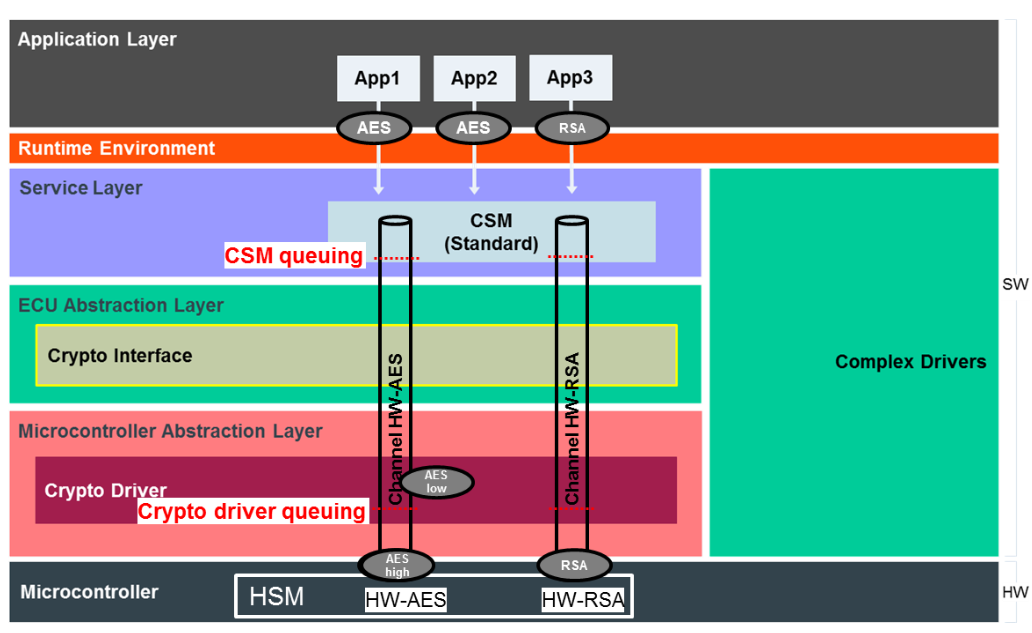
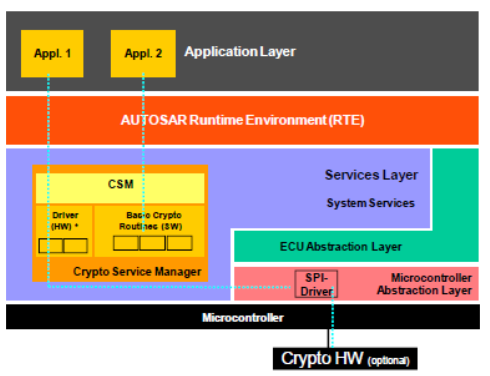
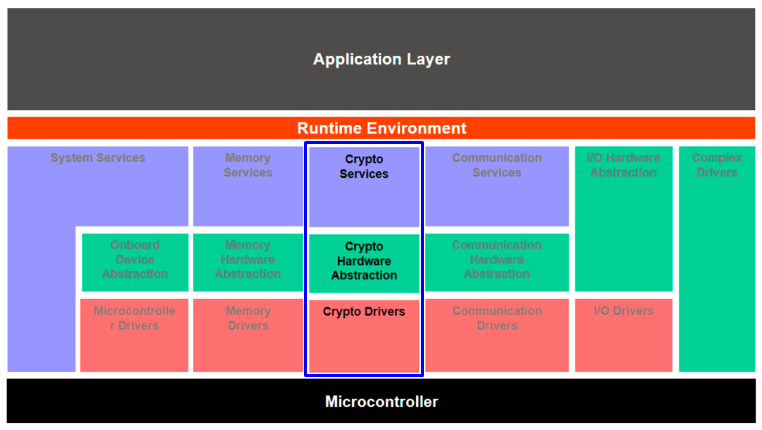
What are hardware security modules (HSM), why we need them and how they work.This is an implementation of the AUTOSAR Crypto Service Manager, compliant with the AUTOSAR standard. The code is documented through comments in the source. Crypto Service Manager (CSM) is the service module from BSW that manages Crypto services (such as description of keys, generation of random. The Autosar cryptography cluster is composed by the following modules: Crypto Service Manager (CSM): This module communicates with the.